Today, Imperva Bot Management (formerly Distil Networks) announced a significant improvement in the device fingerprinting capabilities of its Bot mitigation product. This innovation of the first ever Hi-Def fingerprint goes beyond the IP address and identifies devices with more accuracy and provides the clearest view of web traffic in the bot mitigation industry.
Identification is Difficult
To understand how difficult it is to find a unique identifier, just ask Alphonse Bertillon. He was a French police officer who was the inventor of the mugshot. In fact, this photo of him, is probably the first ever mugshot.
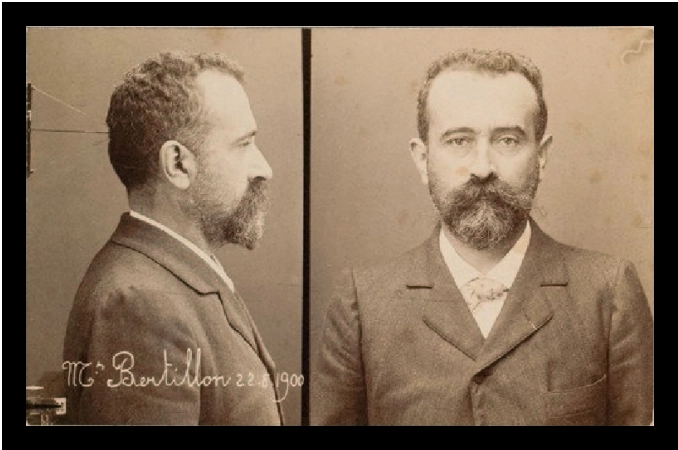
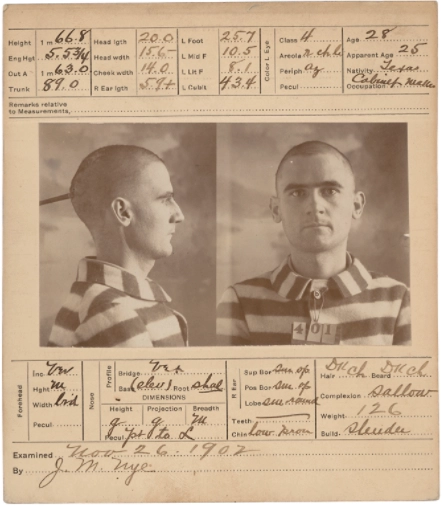
He was also the inventor of another method of identification called the “Bertillon System”. It measured nine parts of the body including left foot, width of head, right ear and height. The information was stored on what was called a Bertillon Card with the mugshot.
At that time, it was thought that this collection of measurements was the unique identifier to identify criminals, until the case of Will West.\
Will West, while being admitted to Leavenworth Prison in 1903, was asked by the admitting clerk if he had been in prison previously. He stated that he had not. The clerk didn’t believe him and checked to see if there was a Bertillon card for him. The clerk found one for a William West and assumed that was him. The clerk challenged Will West and showed him the photo. He agreed that the photo looked like him but remained adamant that it was someone else.
What they were looking at was the mugshot for William West who was already in the prison serving a life sentence for murder. Both men looked alike, had similar names, and near identical bertillon measurements. The only unique identifier was their fingerprints.
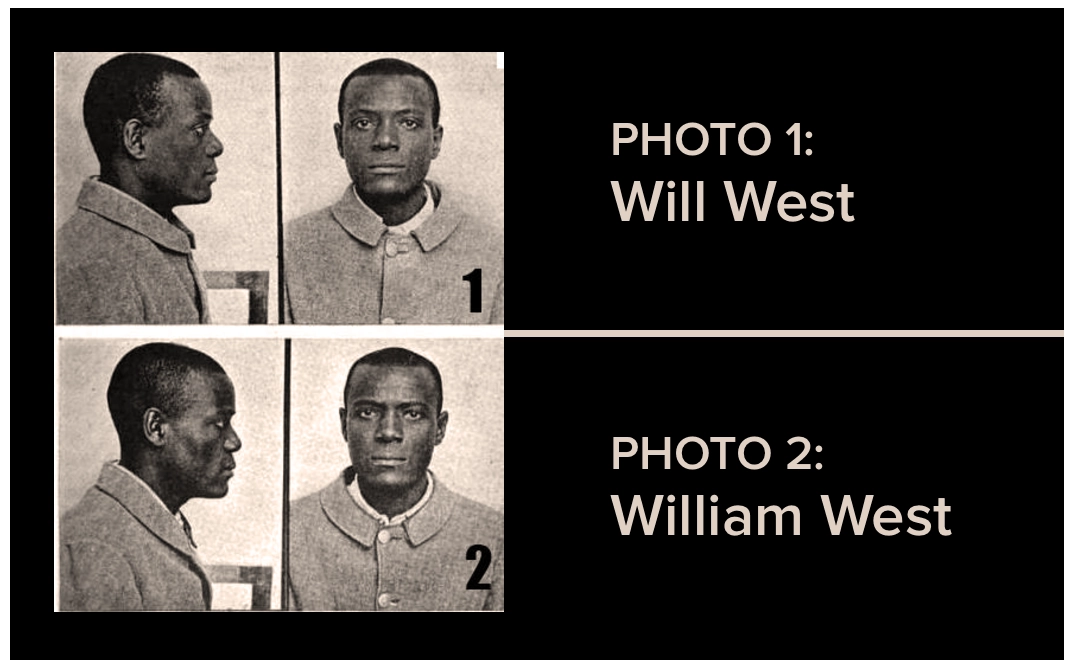
This was the beginning of the end for the Bertillon system. It gave way to fingerprinting as a technique in forensics and today fingerprinting has been improved upon by other techniques like DNA analysis. The journey to accurate identification is all about minimizing both false positives and false negatives.
Not All Device Fingerprints are Created Equal
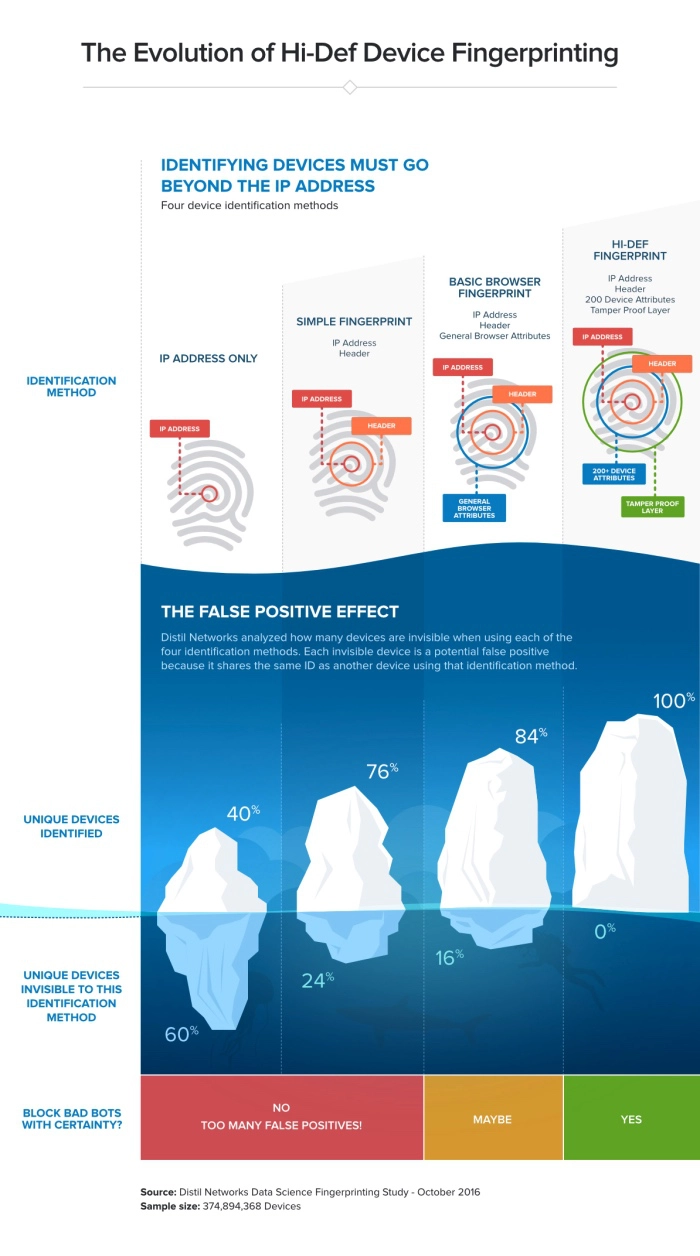
Today, the evolution of identification has taken a similar journey within computer science. The IP address is the equivalent of the Bertillon system. Using an IP address with some header information was the first simple fingerprint. Basic browser fingerprints increased accuracy further by including more device attributes, pushed by the browser, within the identifier. Imperva’s Hi-Def fingerprint is the latest evolution and actively pulls over 200 additional attributes from the device to create the most accurate identifier in the bot mitigation industry.
Security professionals understand philosophically that the IP address is not granular enough but accurate comparison evidence is sparse. But today, Imperva has released a study from its data science team providing actual data on the accuracy of three device fingerprinting techniques compared with Imperva’s Hi-Def Fingerprint. The four fingerprinting techniques are:
- IP address only
- Simple fingerprint (IP address & Header information)
- Basic browser fingerprint (IP address & header information & Select Device attributes).
- Hi-Def fingerprint (IP address & header information & 200+ device attributes)
The study examined almost 375 million device fingerprints and illustrates how many devices would be hidden by each technique in comparison to Imperva’s Bot Management Hi-Def fingerprint. That means the hidden devices would effectively be potential false positives because their identifier is not granular enough. This provides clear real world data to explain why many security solutions in the bot industry are reluctant to enforce the ultimate sanction and block a device because they know that their fingerprint is not accurate enough.
| Fingerprinting Technique | # of unique devices identified | % of unique devices hidden (false positive) |
|---|---|---|
| Imperva Hi-Def fingerprint | 374,894,368 | 0% |
| Basic browser fingerprint | 313,301,312 | 16.4% |
| Simple fingerprint | 275,783,744 | 26.4% |
| IP address only | 149,945,280 | 60.0% |
The infographic below illustrates the stark difference in accuracy between each technique.
Companies looking to prevent bots must ask their vendors which fingerprinting technique they use to identify the device on their website. In a world where accuracy matters, it makes more sense to use the most accurate fingerprinting technique in the bot mitigation industry.
Imperva’s Hi-Def Fingerprinting technology:
- Inspects traffic at the perimeter, identifies malicious devices, and intercepts bad bots before they can wreak havoc on a website
- Fingerprints stick to the bot even if it attempts to reconnect from random IP addresses or hide behind peer-to-peer networks or anonymous proxies
- Goes well beyond IP- and header-centric identification by analyzing over 200 additional device attributes
- Includes a tamper proofing layer, which detects manipulation of data values inside the fingerprint
- Gives users complete visibility into false positives
- Shares the hi-def fingerprint across Imperva customers in a globally-distributed, known violators database, and is made available for other security products like SIEM
As Alphonse Bertillon found out, there are new identification techniques that surpass older techniques in terms of accuracy. And when you are dealing with bad behavior a false positive is a problem that must be minimized. The search for the unique identifier is never ending in criminology and in computing the journey continues. But at least in the identification of bots on your website, Imperva is leading the way with the most accurate Hi-def fingerprint in the bot mitigation industry.
Try Imperva for Free
Protect your business for 30 days on Imperva.