What is API Security?
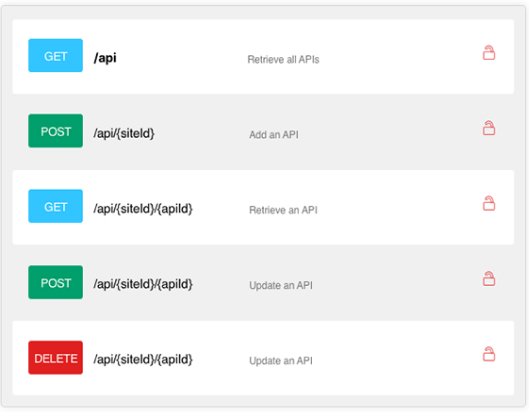
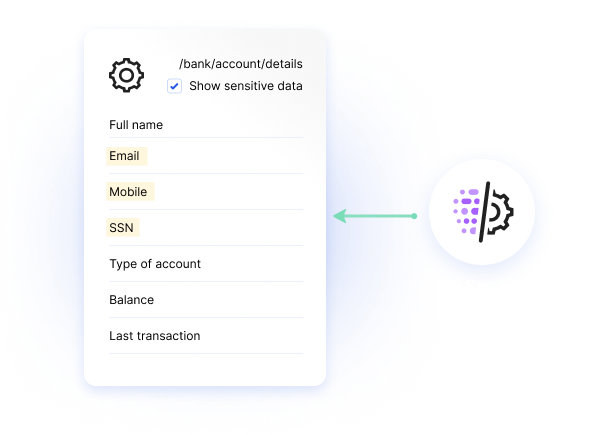
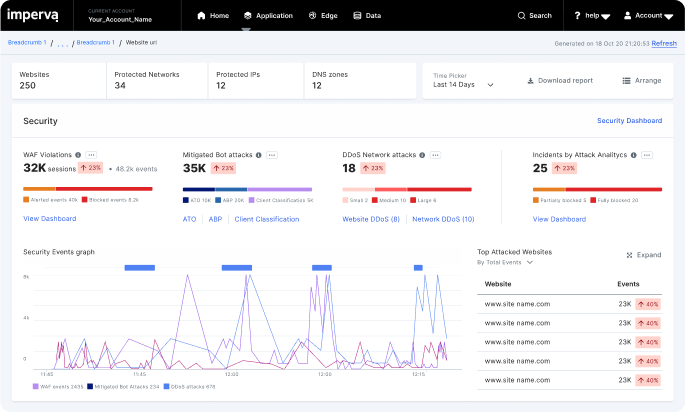
Imperva API Security provides continuous protection of all APIs using deep discovery and classification to detect all public, private and shadow APIs. It also protects against business logic attacks and many more of the OWASP API Top Ten threats. The easy-to-deploy solution empowers security teams to implement a positive API security model.